Chat
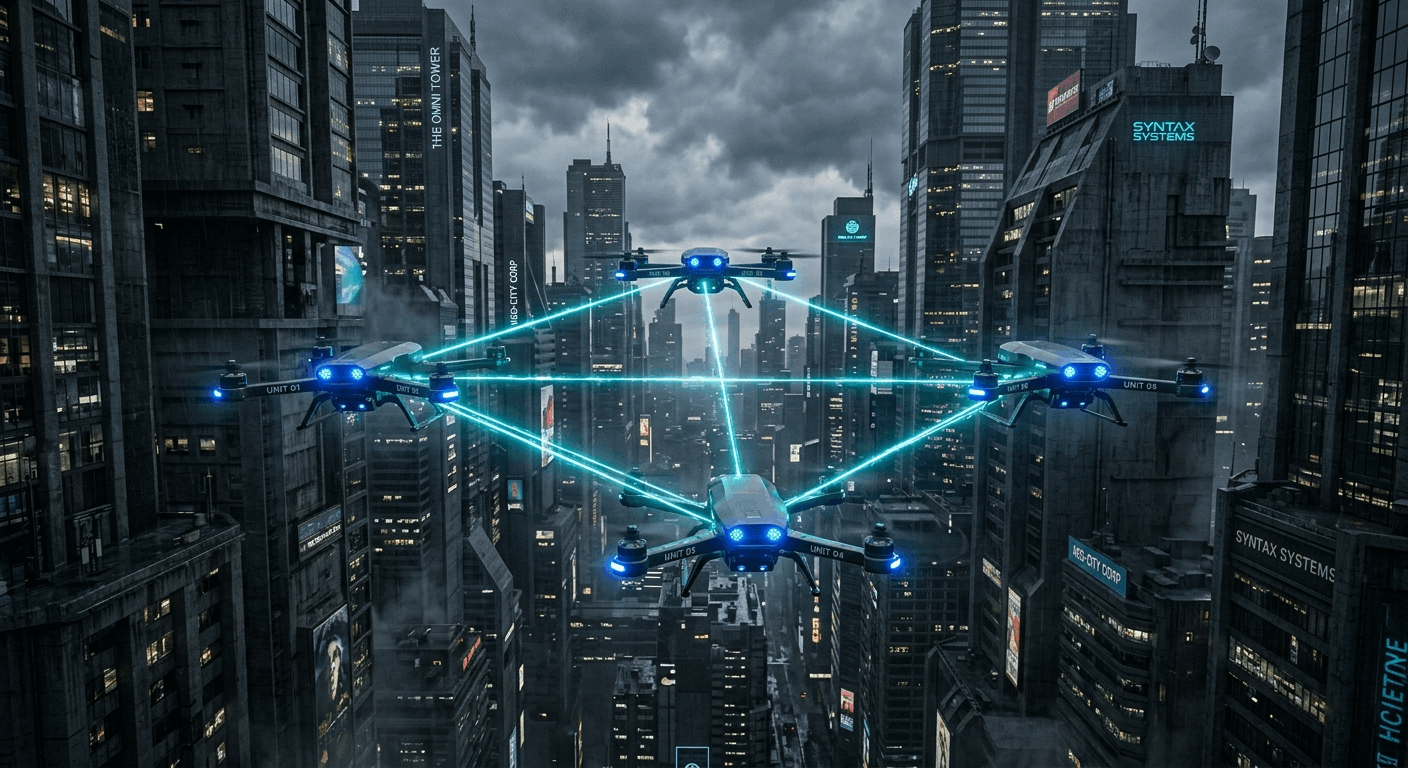
Decentralized Coordination and Acoustic Localization in Secure Autonomous Drone Swarms
This paper presents a fully implemented and experimentally validated decentralized autonomous drone swarm system designed for GPS-denied, vision-impaired, and electronically contested environments. It integrates six tightly coupled subsystems including a Byzantine fault-tolerant leader election protocol (MCSS), AES-256-GCM encrypted mesh communication, ML-enhanced obstacle avoidance, GCC-PHAT acoustic TDOA localization, a distributed cryptographic flight ledger (Flying Ledger), and a C++ Differential Immune System for motor fault resilience demonstrating robust, real-time swarm coordination without centralized control or GPS dependency.
Publication Overview
Publication links, citation access, authorship, and scholarly metadata in one place
This detail page is server-rendered for search visibility and includes structured data so each publication can stand on its own as a fully indexable portfolio entry.
Unmanned Aerial Vehicle (UAV) swarm systems have rapidly advanced from experimental research platforms into mission-critical tools for applications spanning defense surveillance, urban search-and-rescue, disaster response, precision agriculture, and infrastructure inspection. However, most existing architectures depend heavily on centralized control nodes, persistent GNSS availability, reliable communication channels, and benign electromagnetic conditions introducing systemic vulnerabilities in adversarial or degraded operational environments.
This paper addresses these limitations through the design and full implementation of a decentralized swarm architecture engineered for operational resilience. The resulting framework integrates six interdependent subsystems that collectively enhance fault tolerance, secure communication, navigation robustness, and actuator resilience.
System Architecture
The proposed system adopts a layered, modular architecture. At the highest level, a PyQt5-based operator console provides mission supervision. Below this, the SwarmManager orchestrates decentralized swarm behavior, leader election, and inter-drone synchronization. Supporting modules include the distributed Flying Ledger, acoustic TDOA localization engine, ML-based obstacle avoidance, dynamic obstacle modeling, and the encrypted communication layer. At the lowest level, a C++ Hardware Abstraction Layer (HAL) interfaces with the MAVLink/PX4 flight controller for real-time motor control and sensor integration.
The software stack is divided across two execution domains: Python 3.11+ manages swarm-level logic, ledger operations, ML inference, and the GUI; C++17 handles time-critical flight control and latency supervision. Inter-process communication between Python and C++ is implemented via shared-memory IPC with timestamp-annotated packets.
Leader Election — MCSS Protocol
The Multi-Criteria Suitability Scoring (MCSS) protocol assigns each candidate drone a scalar suitability score computed as a weighted aggregation of normalized battery state-of-charge, Motor Health Index, and link quality:
S_i = ω_B·B̂_i + ω_M·M̂_i + ω_L·L̂_i
Default weights are ω_B = 0.4, ω_M = 0.4, ω_L = 0.2. The drone with the highest score is elected leader. Re-election is triggered automatically after two missed heartbeat signals, completing within approximately 1.2 seconds. The protocol tolerates up to ⌊(N−1)/3⌋ Byzantine nodes, consistent with classical distributed fault-tolerance bounds.
Secure Communication — AES-256-GCM Mesh
All inter-drone control and telemetry messages are protected using AES-256 in Galois/Counter Mode (GCM), with swarm keys derived via PBKDF2-HMAC-SHA256 (100,000 iterations). Each encrypted packet follows the structure [IV | Ciphertext | AuthTag]. Replay attacks are prevented using per-sender monotonically increasing sequence numbers embedded as Additional Authenticated Data (AAD), with receivers discarding any messages failing strict ordering validation.
Dynamic Obstacle Avoidance
The obstacle avoidance engine combines three mechanisms: a geometric collision-cone formulation estimating collision risk based on relative position and velocity; a second-order kinematic predictor supporting linear, circular, and random-walk motion models over a 3-second horizon; and acceleration-limited velocity blending for smooth trajectory transitions. An exponential smoothing-based risk memory score accumulates behavioral history per obstacle, increasing avoidance sensitivity for persistently erratic objects.
Acoustic TDOA Localization — GCC-PHAT
The acoustic localization subsystem uses the Generalized Cross-Correlation with Phase Transform (GCC-PHAT) method to estimate inter-drone acoustic propagation delay. Each estimated time delay corresponds to a hyperbolic distance constraint. With three or more non-collinear sensors, the source position is resolved using non-linear least-squares minimization (SciPy's Trust-Region Reflective solver with soft-L1 loss). A latency-aware fallback reduces sensor subset size when C++↔Python round-trip time exceeds 280 ms. Experimental validation demonstrates sub-3 m localization accuracy under moderate noise and wind speeds up to 8.0 m/s.
The Flying Ledger — Distributed Blockchain Audit
Each telemetry event is captured in a cryptographically chained block containing SHA3-256 hashes of telemetry snapshots and event payloads, a reference to the previous block hash, and an Ed25519 digital signature (64-byte, deterministic, Curve25519-based). Blocks are asynchronously broadcast to peer nodes, where each peer validates sequential index consistency, hash-chain linkage, and signature authenticity before appending to its local ledger. Tamper detection is deterministic: any modification to a block propagates hash inconsistency through all subsequent blocks. Consensus tests across three ledger instances confirmed successful replication and rejection of forged blocks.
C++ Differential Immune System
The Differential Immune System continuously monitors per-motor RPM deviation, vibration magnitude, and temperature. A motor is classified as DEGRADED when RPM variance exceeds 10% persistently across a rolling observation window. Upon detection, the system performs geometry-aware thrust redistribution — prioritizing the diametrically opposite rotor — smoothed through a low-pass filter to prevent torque transients. Adaptive PID retuning reduces proportional gain and increases derivative gain on affected axes. Simultaneous multi-motor failure triggers automatic Return-to-Launch (RTL). Stable flight was demonstrated under up to 30% motor degradation with end-to-end control latency below 50 ms.
Experimental Results Summary
| Metric | Baseline Swarm | Proposed Framework | Improvement |
|---|---|---|---|
| Localization | GNSS/IMU | Acoustic TDOA + ML | GPS-Independent |
| Security | None (Cleartext) | AES-256-GCM + Ed25519 | Tamper-Evident |
| CPU Overhead | 42–45% | 57–60% | +15.8% (Security) |
| Leader Failover | ~2,500 ms | 120 ms | 95.2% Faster |
| Wind Resilience | 4.5 m/s | 8.0 m/s | 77% Higher |
| Audit Integrity | Centralized Logger | Distributed Ledger | Byzantine-Resilient |
This work demonstrates a production-level, experimentally validated decentralized swarm architecture that operates robustly in GPS-denied, vision-impaired, and electronically contested environments. By integrating MCSS-based Byzantine fault tolerance, AES-256-GCM encrypted communication, ML-enhanced obstacle avoidance, GCC-PHAT acoustic localization, a distributed cryptographic flight ledger, and a self-healing motor control system, the framework achieves rapid failover, secure coordination, and environmental resilience without relying on any centralized node or GPS infrastructure. All mathematical models are directly mapped to production-level source code, ensuring full traceability between theoretical formulation and implementation.
Research Discussion
Comments and replies
Leave a Comment